About KlustAIR
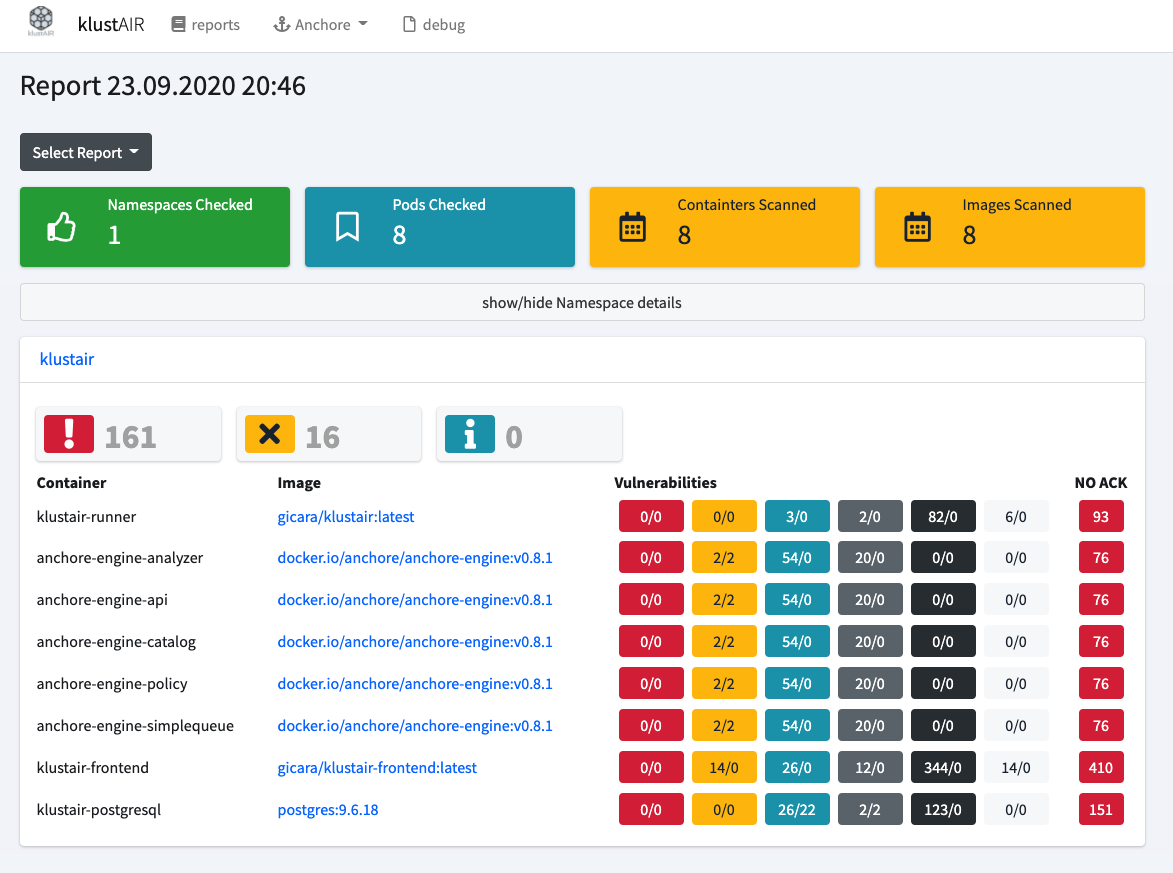
Most vulnerability scanner are part of a deployment pipeline. But what about the containers you started with a Helm chart?
The Klustair runner searches your current Kubernetes configuration for the used images and runs a Trivy scan on them. This allows Klustair to scan also the images used in external Helm charts.
The results are stored in the database. This allows you to compare how the image has evolved between each report.
Releases
Stars
Contributors
Watchers
Repositories
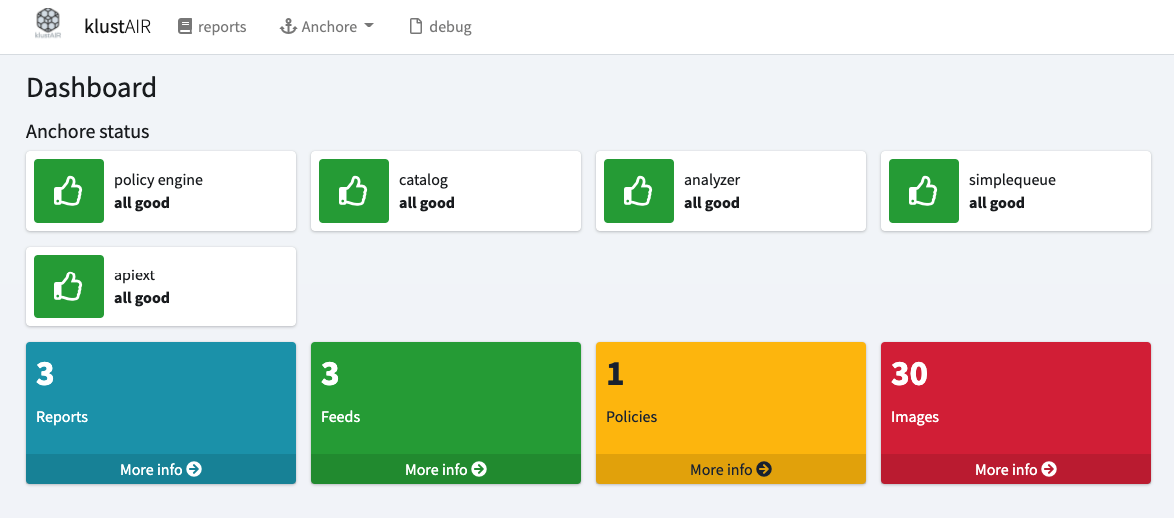
klustAIR comes with 3 repositories:
Scanner
Analyse Your current running Kubernetes setup and generate a report
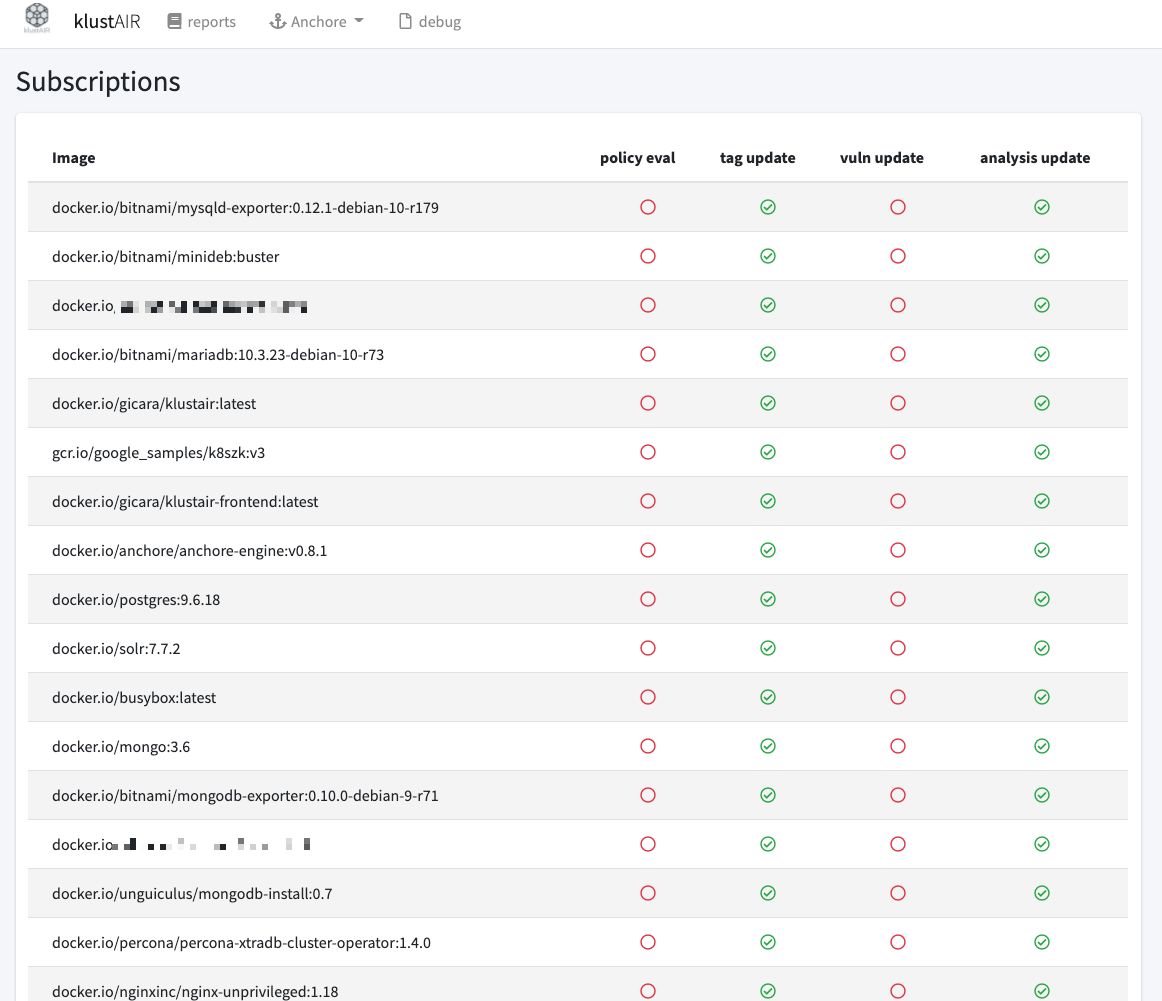
Frontend
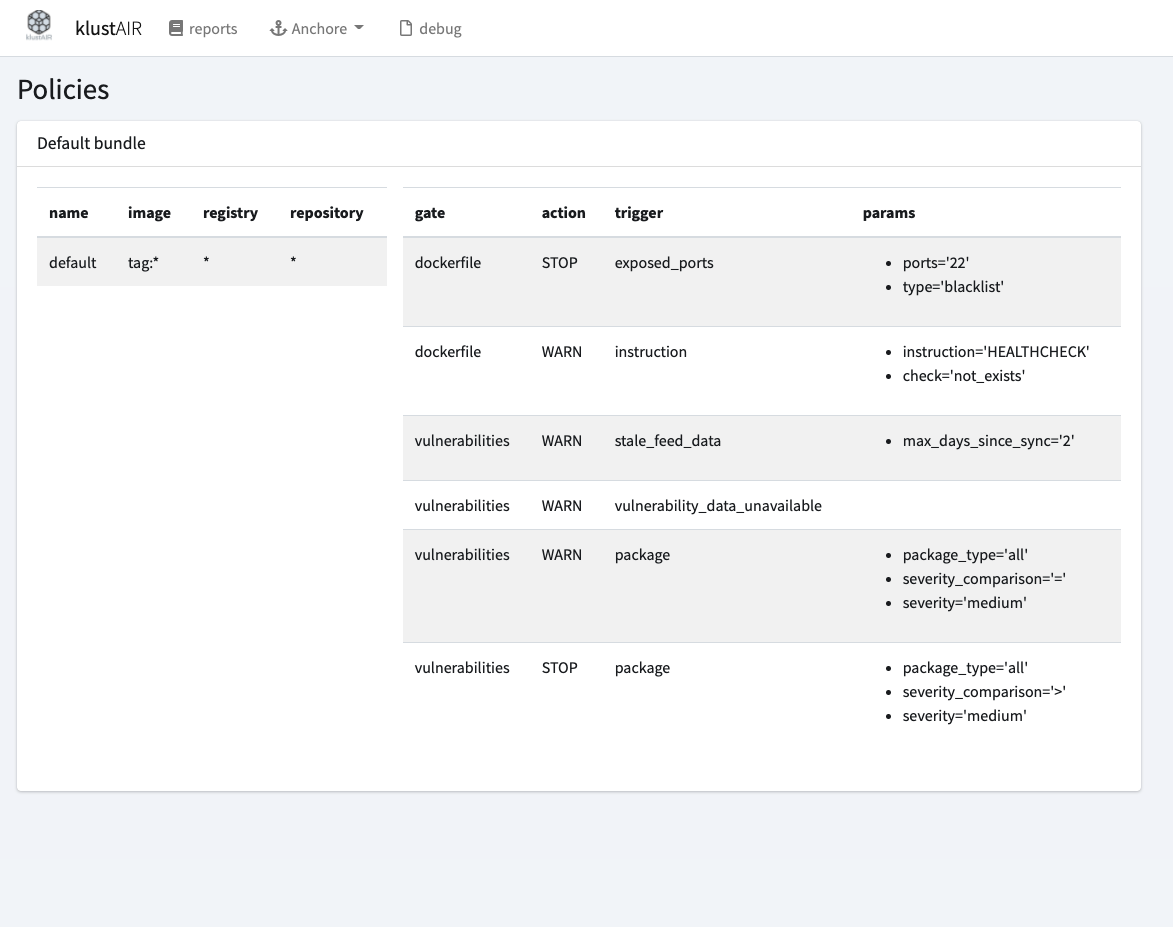
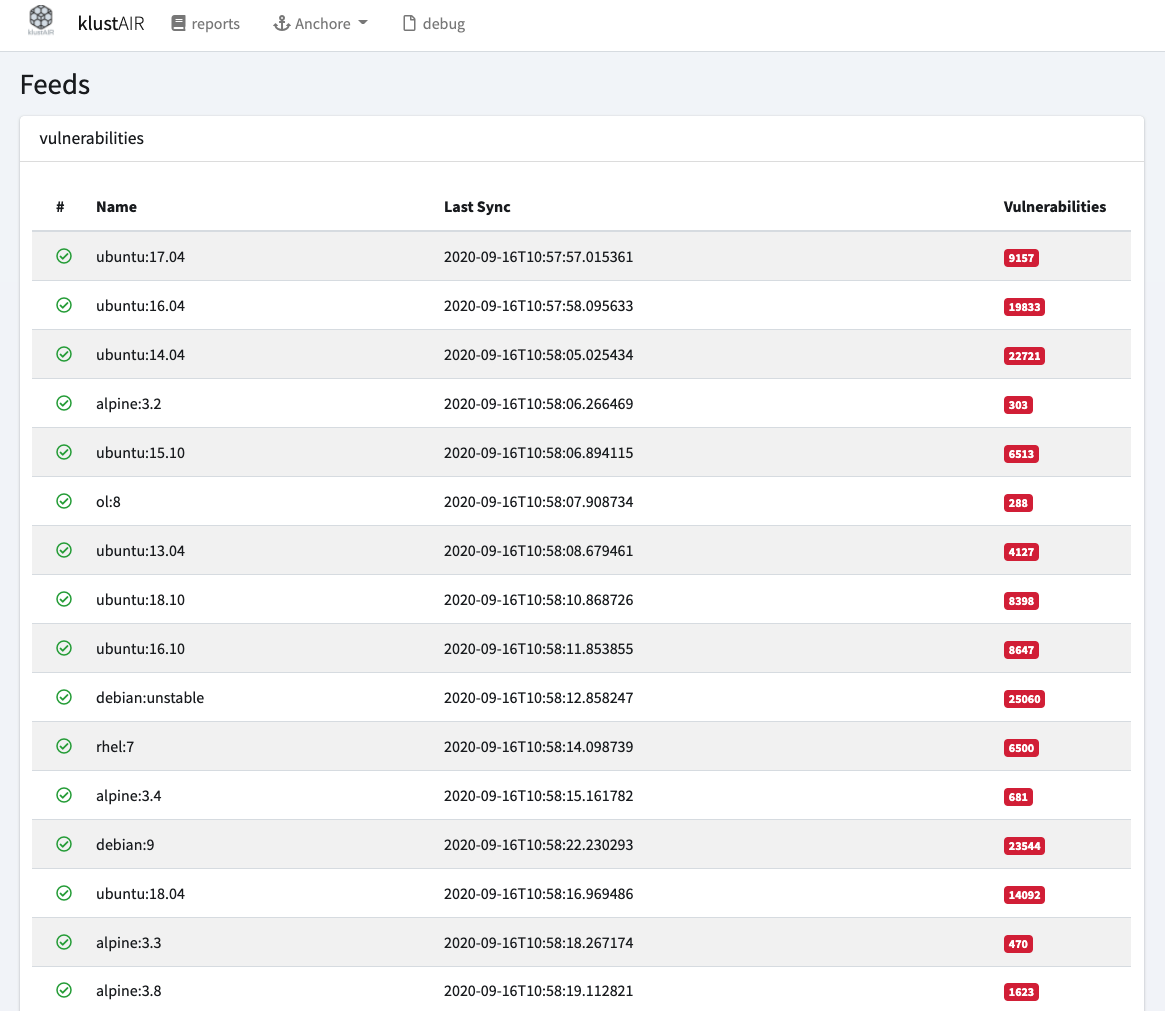
View Your reports and maintain the vulnerabilities.
Helm Chart
Spin up Your installation on Your Kubernetes cluster
Want to support me?
klustAir is completly free of charge. But as a DevSecOp and coffee enthusiast I drink a lot of coffee. So if You buy me coffee, I will appriciate that.
Frequently Asked Questions
If your question is not answered here, feel free to open a issue on Github
-
Can I run the klustAIR runner without a container?
Sure. You can trigger klustair on your local machine. All you need is access to Your Kubernetes cluster (via kubectl) and access the Klustair database to store the result.
-
How do I secure my Klustair frontend?
KlustAIR does not provide any authentication yet. If You want to secure the userinterface you have to do it with Ingress annotations.
-
Is there any support/service I can book?
No.